- Apr 19, 2026
Serious Cybersecurity Risk Found in Popular Car Manufacturer’s Online Portal
- Aug 11, 2025
- Technology
A security researcher discovered a major security vulnerability in the online dealership portal of a popular car manufacturer, which exposed users' personal information and car data, and also allowed hackers to remotely control the vehicles.
Eaton Zveare, a security researcher at a software company named Harness, revealed that the vulnerability he found allowed the creation of an admin account, granting “unlimited access” to the car manufacturer’s central web portal.
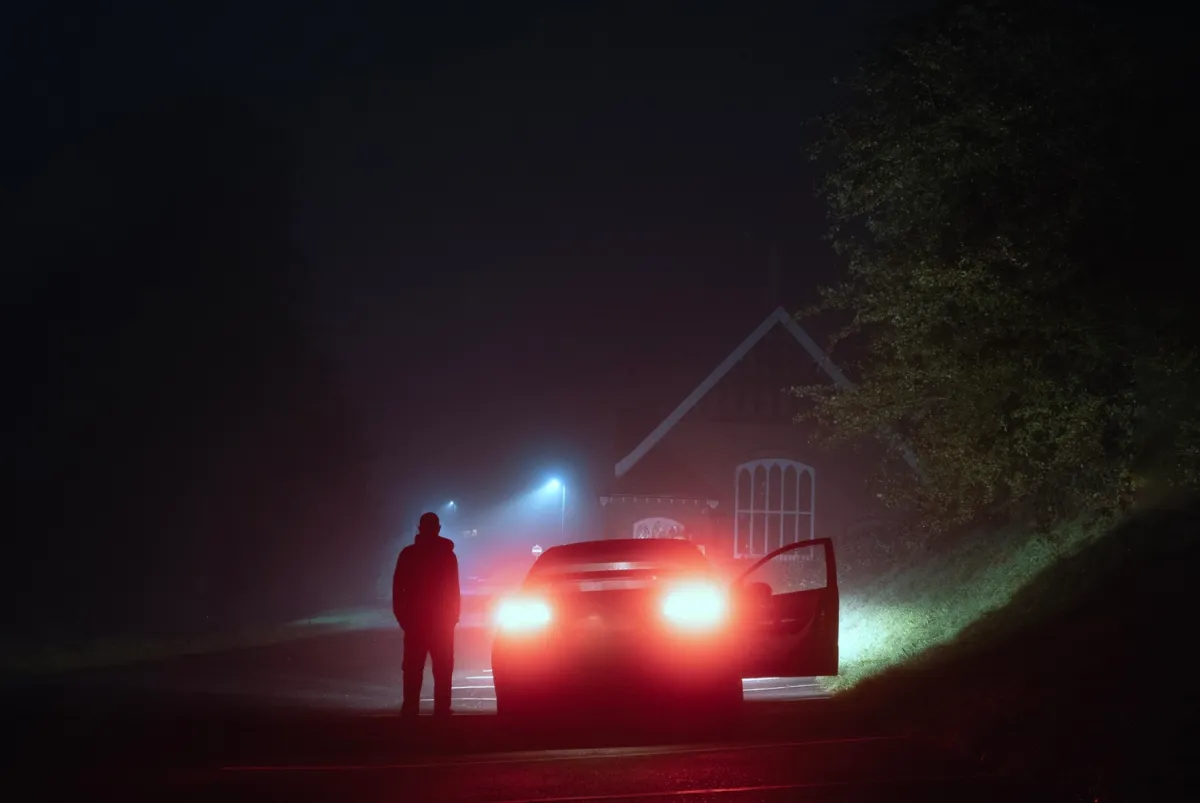
With this access, a malicious hacker could view customers’ personal and financial information, track the real-time location of cars, and even remotely control certain car functions such as locking or unlocking doors.
Zveare discovered this security flaw as part of a weekly project in early 2025. The login system had a flaw that enabled him to create a “national admin” account without logging in.
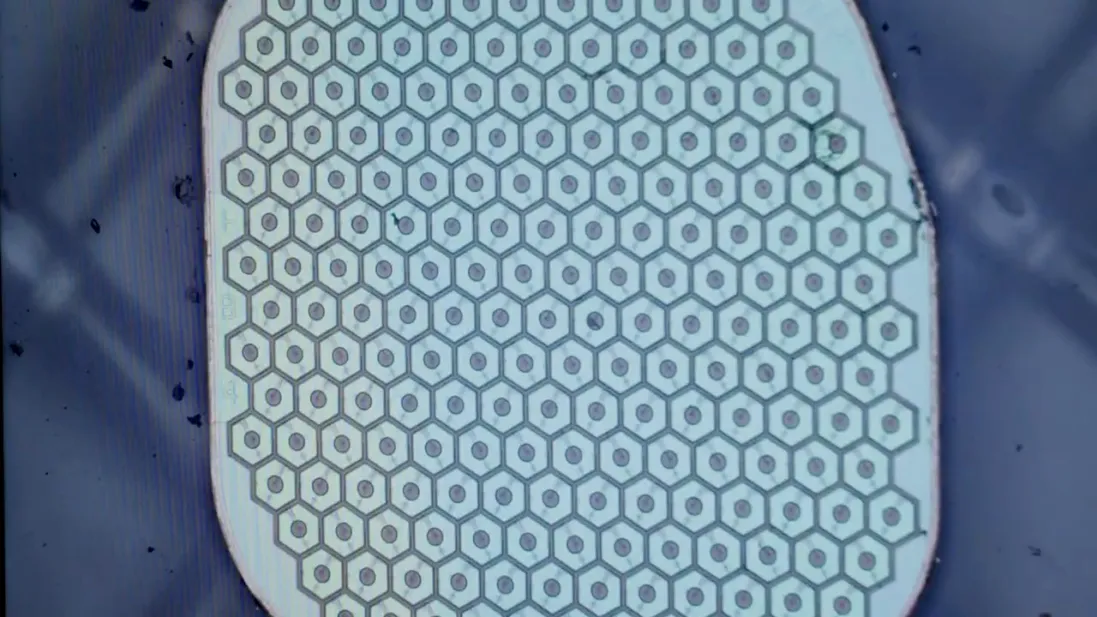
The root cause was that some code on the login page loaded into the browser could be altered by the user, allowing the login process to be bypassed. The car manufacturer later found no evidence of hacking attempts, so it is believed that Zveare was the first to find and report the vulnerability.
Logging into the account gave access to data from more than 1,000 dealerships nationwide. Zveare said, “No one would even notice that you’re able to see all the dealers’ financial and personal information.”
He noted that the portal had a national consumer lookup tool allowing anyone to obtain personal data of the car owner and driver by entering the vehicle number. Zveare gave a real example where he identified the owner of a car parked in a public lot just by using its number.
Through the portal, any car could be linked to a mobile account, enabling owners to open or lock car doors remotely via an app. Zveare tested this method with a friend’s permission. The portal relied on the user’s goodwill, which he referred to as a “pinky promise.”
He said, “I took ownership of the car with my friend’s consent, but in reality, anyone with just a name could have done this.”
Another serious issue was a single sign-on (SSO) feature that allowed one account to easily access other dealership systems. This meant admins could impersonate other users within the system. Zveare had seen a similar feature on Toyota’s dealership portal in 2023.
He described these as “truly terrifying vulnerabilities” from a security standpoint.
Once inside the portal, Zveare gained access to customers’ personal information, some financial data, and real-time vehicle tracking. However, he did not perform sensitive actions like canceling car shipments.
After reporting the vulnerabilities to the car manufacturer in February 2025, they were fixed within a week.
Zveare said, “The main problem was just two API vulnerabilities that compromised login security. When login security fails, everything falls apart.”
Source: TechCrunch